IBM App Connect Enterprise and IBM Integration Bus are vulnerable to arbitrary code execution due to node.js minimist module ( CVE-2022-44906)
Summary
IBM App Connect Enterprise and IBM Integration Bus are vulnerable to arbitrary code execution due to the node.js minimist module ( CVE-2022-44906). A mitigation has been provided for IBM Integration Bus. The latest fix packs for IBM App Connect Enterprise includes minimist 1.2.6
Vulnerability Details
CVEID: CVE-2021-44906 DESCRIPTION: Node.js Minimist module could allow a remote attacker to execute arbitrary code on the system, caused by a prototype pollution in setKey() function in the index.js script. By sending a specially-crafted request, an attacker could exploit this vulnerability to execute arbitrary code on the system. CVSS Base score: 5.6 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/222195 for the current score. CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:L/A:L)
Affected Products and Versions Affected Product(s) Version(s) IBM App Connect Enterprise 12.0.1.0 – 12.0.3.0 IBM App Connect Enterprise 11.0.0.0 – 11.0.0.17 IBM Integration Bus 10.0.0.0 – 10.0.0.26 […]
Click here to view original web page at www.ibm.com
IBM Integration Bus and IBM App Connect Enterprise are vulnerable to arbitrary code execution due to async ( CVE-2021-43138) and nconf (CVE-2022-21803)
Summary
IBM Integration Bus and IBM App Connect Enterprise are vulnerable to arbitrary code execution, due to the async (CVE-2021-43138) and nconf (CVE-2022-21803) modules for Node.js. A mitigation has been provided for IBM Integration Bus. The latest fix packs for IBM App Connect Enterprise includes async >=3.2.3 and nconf 0.12.0
Vulnerability Details
CVEID: CVE-2021-43138 DESCRIPTION: Async could allow a remote attacker to execute arbitrary code on the system, caused by prototype pollution in the mapValues() method. By persuading a victim to open a specially-crafted file, an attacker could exploit this vulnerability to execute arbitrary code on the system. CVSS Base score: 7.8 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/223605 for the current score. CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H) CVEID: CVE-2022-21803 DESCRIPTION: Node.js nconf module could allow a remote attacker to execute arbitrary code on the system, caused by a prototype pollution flaw when using the memory engine. By adding or modifying properties of Object.prototype using a __proto__ or constructor payload, an attacker could exploit this vulnerability to execute arbitrary code or cause a denial of service condition on the system. CVSS Base score: 7.3 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/224357 for the current score. CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L) […]
Click here to view original web page at www.ibm.com
IBM App Connect Enterprise and IBM Integration Bus are vulnerable to multiple openSSL vulnerabilities in Node.js (CVE-2022-1434, CVE-2022-1343, CVE-2022-1473)
Summary
IBM App Connect Enterprise and IBM Integration Bus are vulnerable to a man-in-the-middle attack, remote attacker bypassing security restrictions and denial of service due to openSSL vulnerabilities in Node.js (CVE-2022-1434, CVE-2022-1343, CVE-2022-1473). IBM App Connect provides a fix/fix pack including openSSL 1.1.1o. Mitigation steps to disable node.js have been recommended for IBM Integration Bus
Vulnerability Details
CVEID: CVE-2022-1434 DESCRIPTION: OpenSSL is vulnerable to a man-in-the-middle attack, caused by the use of the AAD data as the MAC key in the RC4-MD5 ciphersuite. A remote attacker could exploit this vulnerability to predict the MAC key and launch a man-in-the-middle attack and gain access to the communication channel between endpoints to modify data in transit in such a way that it will pass a MAC integrity check. CVSS Base score: 6.5 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/225617 for the current score. CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:N) CVEID: CVE-2022-1343 DESCRIPTION: OpenSSL could allow a remote attacker to bypass security restrictions, caused by a incorrect verification of response signing certificates by the OCSP_basic_verify function. By sending a specially-crafted request using the OCSP_NOCHECKS flag, an attacker could exploit this vulnerability to forge positive verification results. CVSS Base score: 5.3 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/225618 for the current score. CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:L/A:N) CVEID: CVE-2022-1473 DESCRIPTION: OpenSSL is vulnerable to a denial of service, caused by a resource leakage when decoding certificates and keys by the OPENSSL_LH_flush() function. By sending a specially-crafted request, a remote attacker could exploit this vulnerability to cause a denial of service. CVSS Base score: 5.3 CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/225616 for the current score. CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L)
Affected Products and Versions
IBM strongly recommends addressing the vulnerability/vulnerabilities now by applying the appropriate fix to IBM App Connect Enterprise and mitigation to IBM Integration Bus Affected Product(s) Version(s) IBM App Connect Enterprise 12.0.1.0 – 12.0.4.0 IBM App Connect Enterprise 11.0.0.0 – 11.0.0.18 IBM Integration Bus 10.0.0.0 – 10.0.0.26 (Linux x86-64 and Windows x86-64 only)
Click here to view original web page at www.ibm.com
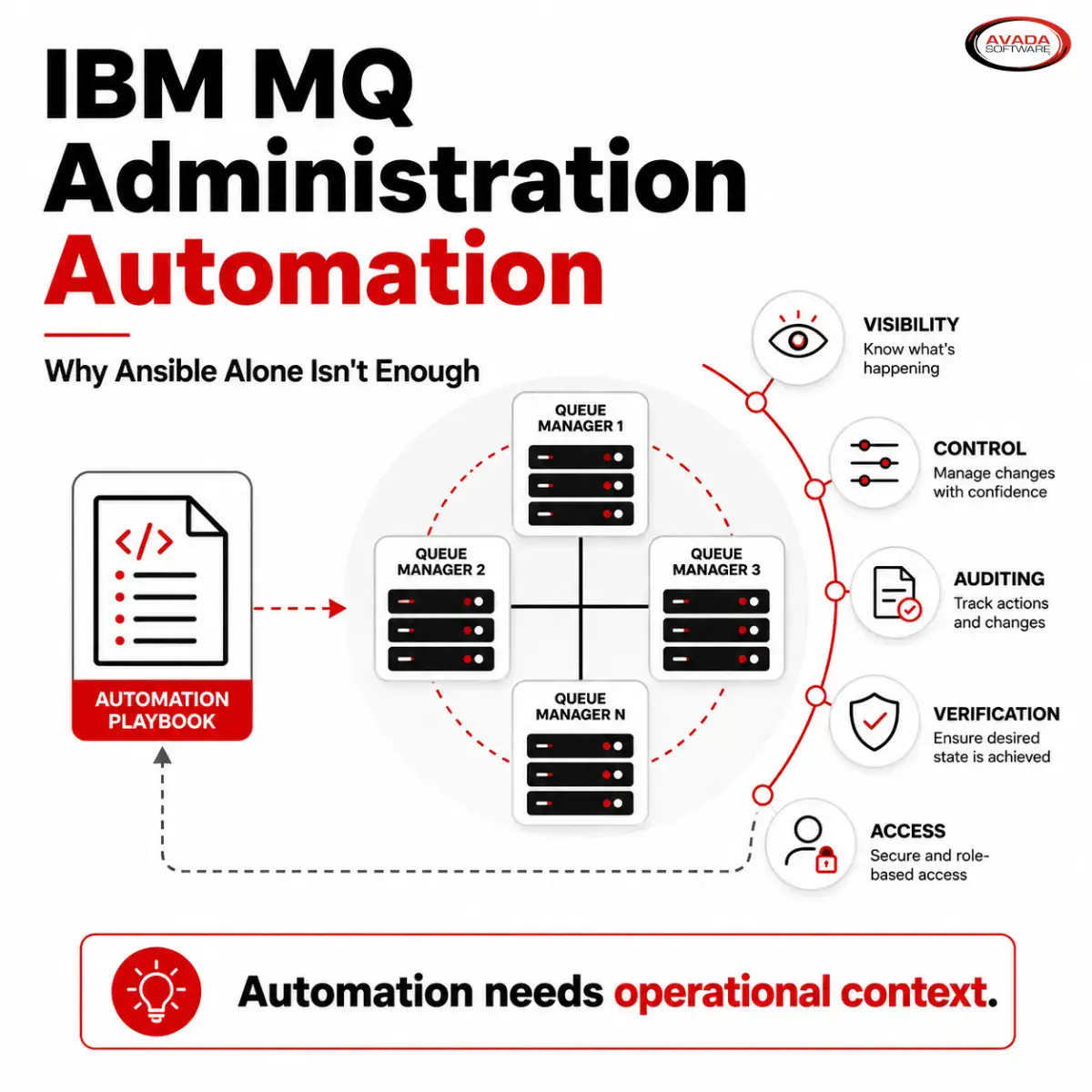
When assessing vulnerability risks you need to include an Inside-Out approach. Infrared360 can help you mitigate inside-out IBM Integration Bus & App Connect vulnerabilities, and all your middleware inside-out vulnerabilities – while giving your middleware team smarter, easier, tools for optimizing performance and meeting SLAs. Check out the information below or our Infrared360 overview.