Avada Software has received a lot of positive reaction to our recent webcast on self-service IT, Improving Productivity Through Smart, Safe, Self-Service. Thank you to all those who attended and commented.
My goal with this blog post is to expand upon the thoughts of that webcast here. One or two of the replies we received stood out because Avada Software has been evangelizing the enablement of self-service IT since our inception in 2006, when the product was built to allow for “delegated administration”. The entire point of delegated administration “is” self-service. But that is not just for individuals, it is intended as a collaborative solution for teams of people. The idea is to delegate to a person, persons, team, project team, dept, etc. exactly what you want them to see and what you need them to do. It’s that simple.
Those particular replies were from people that were “looking for a self-service product”. Well, that term is not exclusive to anyone, but one of the primary reasons for Avada Software’s product, since day one, was to provide that ability. We’re glad that the webcast illuminated that “delegated administration” and “self-service” are synonymous. You can’t have “secure” self-service without being able to delegate to the End User in a way that limits and/or grants visibility and access to exactly what you want them to see and do. Otherwise, you wouldn’t allow them to self- administrate because they’d be able to see any resource and perform any action! In this day of compliance adherence, that would be heresy.
And there was another message that came up loud and clear in the discussion: Compliance and Security.
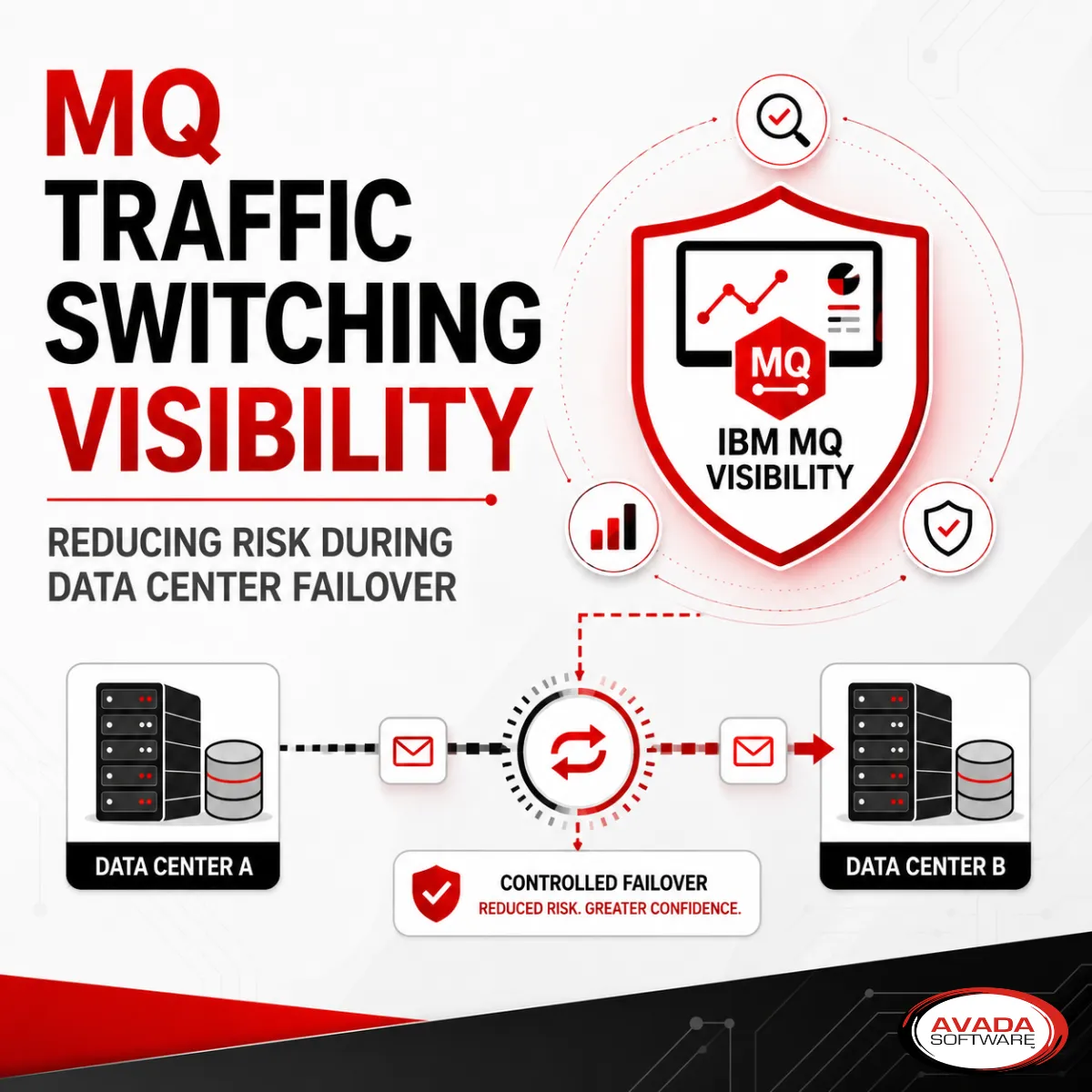
There are many types of security. Most people hear that and think about handshake security, like you need to do with SSL. There’s also authentication security, like you do with LDAP to allow users to Login to their workstation or applications. However, there is also visibility security!
With our Infrared360 middleware management portal, what users aren’t given permission to see, they won’t know exists, and therefore won’t be able to access. In addition, there is policy security: For objects Users are permitted to access, they can only perform certain “allowed” actions – per your policy (determined by their role on that team, project, dept, etc.).
There are two things compliance overlords love about this. One is that you can see and control all User access and permissions before anyone does anything. The other is that in a good self-service IT product, like Infrared360, you can look up or run a report on any User(s) to see what they have access to see, and what they have access to do. Coupling that with an audit trail of actions that have been performed (even if they do have the permission to do so) gives Admins a full 360⁰ view that they can share with Compliance auditors. You can even give them their own log-in that provides them access only to user audit reports and views, enabling them to verify the information they need for the sake of corporate policies.
And that is really the basis of Smart, Safe, Self-Service as noted in the webcast.
Other reading:
Infrared360 recognized as a top enabler of Self-Service IT Administration by CIOReview magazine.