IBM MQ Appliance Authority Vulnerability (CVE-2026-1713) Addressed: What MQ Teams Should Do Now
Security bulletin recap and upgrade checklist for IBM MQ Appliance 9.4 LTS and 9.4 CD
Key takeaways
- IBM disclosed and addressed an authority vulnerability affecting IBM MQ Appliance (CVE-2026-1713).12
- The issue relates to unintended access to the system queue SYSTEM.AUTH.DATA.QUEUE, which stores MQ authorization data.14
- Affected appliance streams: 9.4 LTS (9.4.0.0–9.4.0.17) and 9.4 CD (9.4.1.0–9.4.4.1).1
- IBM states there are no workarounds; remediate by upgrading to 9.4.0.20+ (LTS) or 9.4.5.0+ (CD).156
What IBM announced
On February 18, 2026, IBM published a security bulletin stating that IBM MQ Appliance has addressed an authority vulnerability tracked as CVE-2026-1713. For clarity: while the bulletin’s description says “IBM MQ is affected…”, the affected versions and fixes are delivered as IBM MQ Appliance firmware levels—so this is best read as an IBM MQ Appliance issue (in the IBM MQ component shipped with the appliance).1
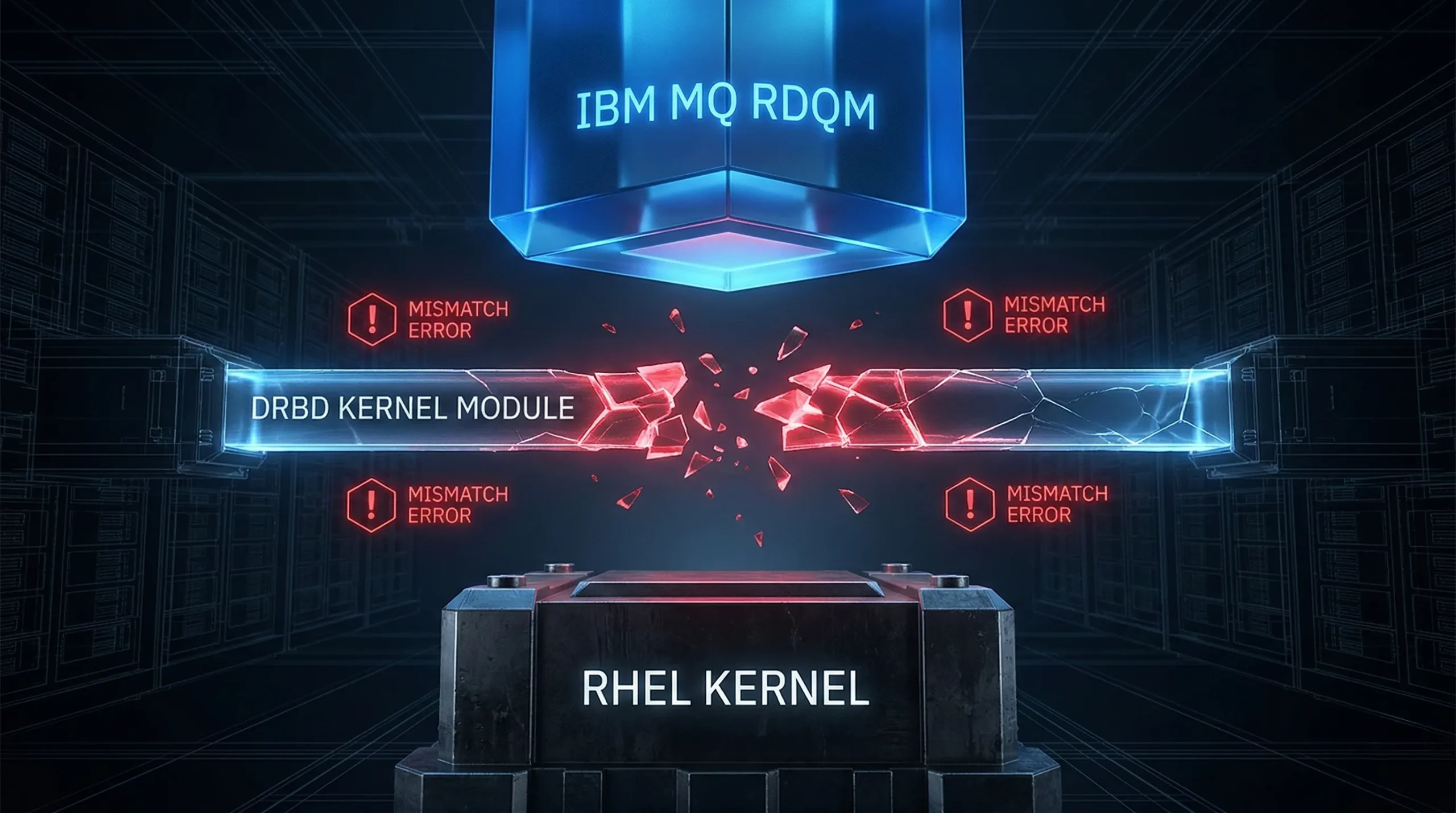
What’s the vulnerability?
IBM describes an authority vulnerability that could allow a user to access SYSTEM.AUTH.DATA.QUEUE. IBM maps the weakness to CWE-305 and reports a CVSS v3.1 base score of 5.5 with vector AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N (medium severity).1310
Why SYSTEM.AUTH.DATA.QUEUE matters
In IBM MQ, authorization data is stored on a local system queue named SYSTEM.AUTH.DATA.QUEUE. IBM documents that access to this queue is restricted (for example, to users in the mqm group, with additional constraints on Windows) and that this access cannot be changed. That’s why any defect that expands who can reach this queue deserves attention: it can undermine authorization integrity and the operational controls that depend on it.4
Who is affected
IBM lists the following IBM MQ Appliance streams and version ranges as affected:1
- IBM MQ Appliance 9.4 LTS: 9.4.0.0 through 9.4.0.17
- IBM MQ Appliance 9.4 CD: 9.4.1.0 through 9.4.4.1
Remediation: what to apply
IBM states there are no workarounds or mitigations, and recommends upgrading appliance firmware to a fixed level. The bulletin references known issue DT433340 and points to these minimum fixed levels:1
- 9.4 LTS: apply IBM MQ Appliance cumulative security update 9.4.0.20 (or later).15
- 9.4 CD: apply IBM MQ Appliance continuous delivery release 9.4.5.0 (or later).16
How to check your current appliance level
Before scheduling an update window, confirm what you’re running today:
- At the appliance CLI, use show version to confirm the installed firmware and library versions.7
- From mqcli, run dspmqver -v to confirm the MQ version/build in the appliance environment.8
Upgrade planning (command-line overview)
Exact steps and sequencing vary by your topology (single appliance, HA pair, DR, and so on), but IBM’s command-line documentation highlights the core flow you should expect:9
- Stop queue managers (for example, endmqm queue_manager_name).9
- Upgrade to the new firmware level using the boot image accept-license firmware_file workflow described by IBM.9
- After the appliance restarts, start queue managers (for example, strmqm queue_manager_name) and validate service.9
Tip: Treat this like any other security maintenance release—capture a pre-change “known good” snapshot (version info, key queue manager status, and health checks), then re-run the same checks after the upgrade.
Post-upgrade validation checklist
- Re-run show version and dspmqver -v and record the new command level/build output.78
- Validate channel connectivity, listener status, and application flows that are most sensitive to authorization changes.
- Confirm that administrative access patterns (who can perform MQSC/PCF tasks, who can browse/alter privileged objects) behave as expected.
Stay ahead of future bulletins
IBM provides a subscription service (“My Notifications”) that can email or RSS-deliver security bulletins and other support updates. For security program context, IBM also publishes an overview of its PSIRT process and vulnerability management approach.1213
If you need help locating the right download path or support route in your region, IBM maintains a worldwide contacts directory. IBM also provides a central landing page for browsing security bulletins.1415
Once you’ve applied the recommended firmware level, the next step is making sure your day-to-day operations don’t reintroduce risk. Vulnerabilities get addressed with patches—but security is sustained through tight access controls, clear role separation, and visibility into who changed what and when across your MQ Appliance and broader middleware estate. Infrared360 helps teams operationalize those practices by improving control and oversight of middleware administration activities—so you can standardize how privileged actions are performed, reduce ad-hoc access, and support audit-friendly processes.
To go deeper on the practical side of strengthening MQ authority practices, Read: Access Controls in MQ — Enhancing Incident Response.
Endnotes
- IBM Security Bulletin: “IBM MQ Appliance is affected by an authority vulnerability (CVE-2026-1713)” (node 7261146), created Feb 18, 2026; modified Feb 26, 2026. https://www.ibm.com/support/pages/node/7261146
- CVE Record: CVE-2026-1713 (CVE Program). https://www.cve.org/CVERecord?id=CVE-2026-1713
- CWE-305: Authentication Bypass by Primary Weakness (MITRE CWE). https://cwe.mitre.org/data/definitions/305.html
- IBM MQ documentation: authorization data is stored on SYSTEM.AUTH.DATA.QUEUE; access is restricted (mqm group; additional Windows restrictions) and cannot be changed. https://www.ibm.com/docs/en/ibm-mq/9.2.x?topic=awmoalw-how-access-control-is-implemented-by-mq-aix-linux-windows
- IBM Fix Central entry used by the bulletin for IBM MQ Appliance cumulative security update 9.4.0.20 (LTS). https://www.ibm.com/support/fixcentral/swg/selectFixes?fixids=9.4.0.20-IBM-MQ-Appliance+&function=fixId&includeSupersedes=1&parent=ibm~WebSphere&product=ibm%2FWebSphere%2FIBM+MQ+Appliance+M2000
- IBM Fix Central entry used by the bulletin for IBM MQ Appliance continuous delivery release 9.4.5.0 (CD). https://www.ibm.com/support/fixcentral/swg/selectFixes?fixids=9.4.5.0-IBM-MQ-Appliance+&function=fixId&includeSupersedes=1&parent=ibm~WebSphere&product=ibm%2FWebSphere%2FIBM+MQ+Appliance+M2000
- IBM MQ Appliance command reference: show version displays firmware and library version details. https://www.ibm.com/docs/en/mq-appliance/9.3.x?topic=show-version
- IBM MQ Appliance command reference: dspmqver -v displays MQ version and build information from mqcli. https://www.ibm.com/docs/en/mq-appliance/9.4.x?topic=commands-dspmqver-display-version-information
- IBM MQ Appliance documentation: upgrading by using the command line (example steps include stopping queue managers and booting the new firmware image). https://www.ibm.com/docs/en/mq-appliance/9.4.x?topic=94-upgrading-version-by-using-command-line
- FIRST: Common Vulnerability Scoring System (CVSS) v3.1 User Guide. https://www.first.org/cvss/v3-1/user-guide
- FIRST: CVSS v3.0 Calculator. https://www.first.org/cvss/calculator/3.0
- IBM Support: My Notifications Subscription Service. https://www.ibm.com/support/pages/node/718119
- IBM Trust Center: Security vulnerability management overview (PSIRT process). https://www.ibm.com/trust/security-vulnerability-management
- IBM Worldwide Contacts page. https://www.ibm.com/contact/global
- IBM Product Security Central / Security Bulletins landing page (as linked from the bulletin). https://www.ibm.com/support/pages/bulletin/